Announcing Exploit Scanner 1.0
With the launch of WordPress 3.1 — actually slightly delayed by bug hunting — I am pushing Exploit Scanner version 1.0.
Summary of main changes:
- diffs of modified core WordPress files
- File hashes for WordPress 3.1
- Updated malicious pattern signatures
Core file diffs
The major feature delivered with the new release are diffs of core file changes. This allows you to easily see how a modified file has been changed from the original and identify any malicious code that has been introduced.
These diffs are powered by the same engine that runs the compare revisions feature in WordPress; that is Text Diff from The Horde Project and PHP PEAR.
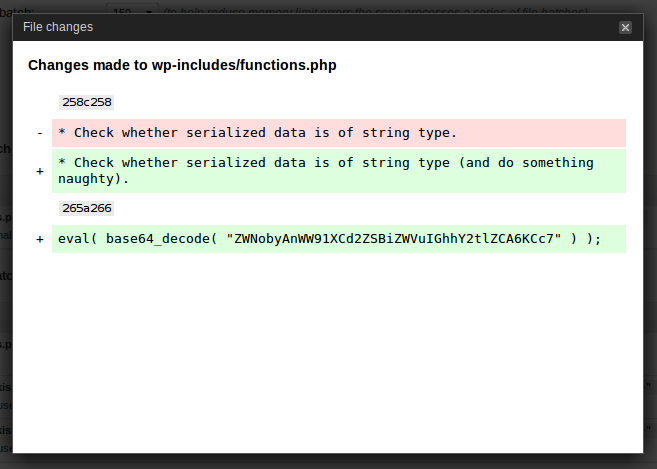
Understanding the output is relatively simple. First of all the pretty colours quickly show you what has been added or removed from the file in question. Red indicates content that has been removed from the original, unmodified core file. Green highlights lines that have been added to a file. There are also reference numbers along with ‘change commands’ detailing the line numbers affected. There are three of these change commands:
- lar — Add the lines in range r of modified file after line l of the original file.
- fct — Replace the lines in range f of the original file with the lines in range t of the modified file.
- rdl — Delete lines in the range r of the original file; line l is the line where they would have appeared in the modified file if they had not been removed.
This feature works by retrieving the unmodified source file from the WordPress subversion repository and comparing it to the local file using Text Diff. Unmodified sources are cached in the database to reduce HTTP requests and (minimal) extra load on the WordPress.org servers.
Plans for the future
Bug fixing and continued core hash updates as usual. Unfortunately people still seem to encounter problems when running scans, but I never seem to be able to reproduce and pinpoint how the error is occurring. 1.0 adds some error catching code to help track this.
wp-config.php tracking. Changes to core files are easily spotted with checksums and the new diffs feature, but the all important wp-config.php file is not tracked. This probably would not be limited to just the config file, but could be extended to all files that make up your WordPress installation (i.e. plugins, themes, etc.) and would allow you to detect any modifications made from a known clean state à la AIDE.
Over the air signature updates and patches are really interesting to me. I have been toying with the idea providing (semi-)automatic updates to the malicious code signatures and even core patches for security vulnerabilities — though the latter may best be left to the VaultPress team (sidenote: is there going to be a public release of the plugin at some point?). This is the least likely update for the near future and would most probably be an optional feature as it would involve pinging an update server. A pipe dream for now.
Let me know if there is anything you would like – or not like – to see in future versions of Exploit Scanner.


